What Are Proxies? Your Go-To Guide in 2026
Learn all about proxies, their types, and main use cases.
By mediating all your connection requests, a proxy server can help you improve anonymity, unblock content limited to specific locations, run a large number of automated tasks, and filter all traffic that goes through it. It’s a very versatile tool used by anyone from individuals and small businesses to large enterprises.
This guide will give you a brief but comprehensive introduction to proxy servers. It explains how proxy servers work, where they’re used, how a proxy differs from a VPN, and more. Most of the structural parts lead to other articles that uncover the topics in greater detail. We hope it will come in handy for you.
Let’s get started.
What Is a Proxy Server?
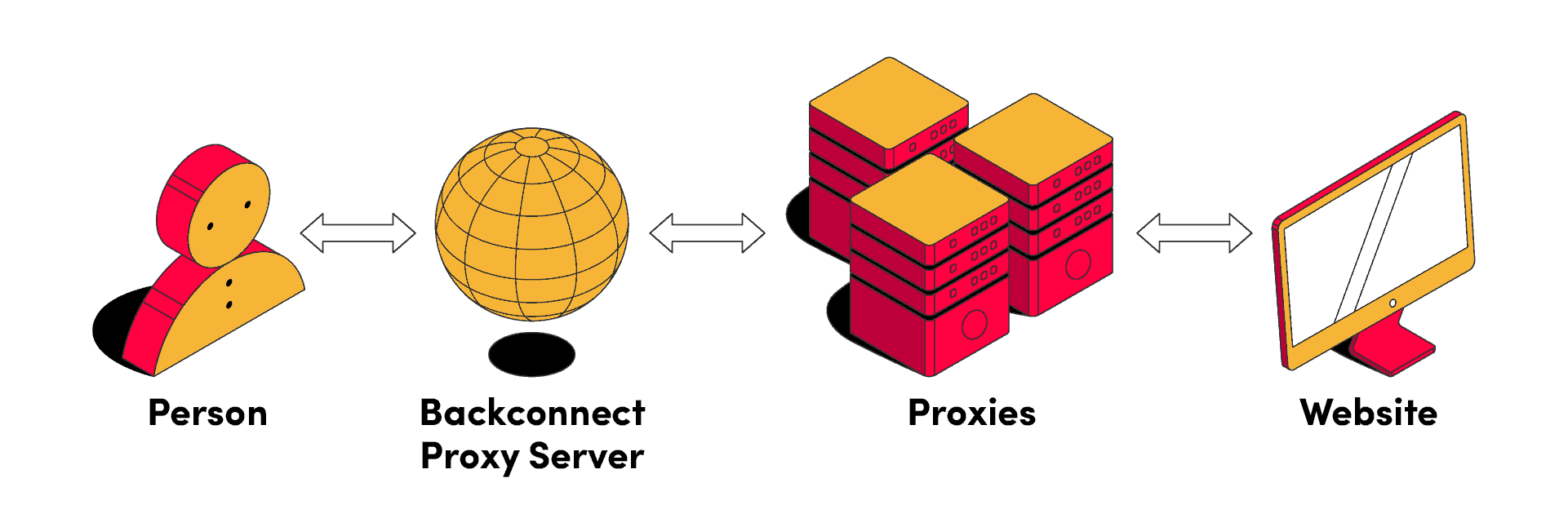
Translated into simpler words, the term proxy server means middleman computer. And that’s exactly what it is: a machine that stands between you and the internet. Instead of connecting to a website directly, a proxy server will route your connection through itself, sending the request on your behalf. It will then return the website’s response, also through itself.
What Are Proxies?
Each internet-connected device has an IP address. It’s a sequence of numbers that identifies the device on a network. Without it, computers wouldn’t be able to communicate with one another – just like a postman couldn’t deliver mail to you without knowing your home address. An IP address holds some additional information about you, such as which company sells you internet access or where approximately your device is located.
In essence, proxies are different IP addresses you receive after connecting to a proxy server. They let you change your identity (to some extent) and location in the eyes of websites. Administrators use proxy servers for different aims, which we’ll talk about in a moment.
Meanwhile, here’s a short video we’ve made about what a proxy is and how it works:
What Are Proxies Used for?
Proxy servers have many powerful uses. First, they can improve your privacy by hiding your original IP address. This is an important feature, but it alone hardly justifies choosing a proxy over, say, a VPN.
Second, you can choose proxy IPs from many locations around the world. Some websites serve different information for specific geographic regions. So, being able to change your perceived location can be very useful both for consuming content and achieving business goals, such as verifying ads or doing market research.
Third, and the most important point – you can use several proxies at the same time to run a large number of automated tasks. Proxy providers offer pools of addresses that constantly rotate, letting you avoid CAPTCHAS and other restrictions. Price aggregation, data scraping, sneaker shopping, and many other jobs would be much harder or even impossible without proxy IPs.
Finally, a reverse proxy server can filter all incoming and outgoing requests. System administrators use them like load balancers to distribute traffic among servers; cache static websites to save resources and improve speed; or, limit access to certain websites like a firewall.
Read more: Why Use a Proxy Server?
Proxy Server vs VPN
At first sight, a proxy looks similar to a Virtual Private Network (VPN). Is it, and if not, what’s the difference?
VPNs and proxies follow the same principle: they put an intermediary between you and the internet. However, people mostly use proxies for bulk tasks, to establish many connections at the same time. On the other hand, VPNs create one connection with increased privacy and security.
Read more: Proxy Server vs VPN.
Main Proxy Server Types
There are several types of proxy servers with different characteristics. These differences could be what makes or breaks your project.
Perhaps the largest distinction is between forward and reverse proxy servers. Forward proxies modify all connection requests leaving your device, while reverse proxy servers intercept all connections reaching a server or a website. Many common proxy use cases, such as web scraping or changing your location, use forward proxy servers.
The second important distinction is based on proxy anonymity. High anonymous proxies (also called elite proxies) hide both your IP address and the fact that you’re using a proxy server. Anonymous proxies hide your IP but reveal that you’re using a proxy. Transparent proxies don’t hide anything. This type is often found in airports and other places with public Wi-FI.
The third major distinction shows proxy origin. Datacenter proxies get their IPs from servers in data centers. They’re very fast and stable but easier to identify as proxy addresses. Residential proxies borrow the IPs from real residential users – their desktop and mobile devices.
Are Proxies Legal?
You’ve probably heard a thing or two about proxies, and they weren’t necessarily positive. In the past, proxy servers were often used as botnets – malware-infected devices – to take down websites, send spam email, or hack credit cards. This might give you an impression that they’re shady or even illegal.
However, proxies themselves are completely legal. While you can’t always be sure where a proxy provider gets its IPs from (especially when it’s residential IPs), the use of proxy servers isn’t prohibited. On the opposite: proxies power many legitimate businesses, such as flight aggregators or price comparison sites.
What matters is how you use proxies. For example, ticket scalping is forbidden in the US, and web scraping is a legal gray area; so, you should always read the website’s policies and the robots.txt file before doing something with it.
Are Proxy Servers Safe to Use?
Proxies are perfectly safe to use, as long as you’re getting them from a reputable provider. Such companies have legal commitments, and it’s in their business interest to keep your data secure. However, you should be very careful with free proxy lists online. They’re not safe and can cause much harm: from injecting ads into pages you visit to outright stealing your personal information.
Read more: The Dangers of Free Proxies.
How Much Do Proxies Cost?
Let’s say you’ve decided to buy some proxy IPs. How much can you expect to pay? The price largely depends on the proxy type.
Datacenter proxies are the cheapest option. Dedicated addresses cost $1-2/IP. If you’re willing to share them, you can get the price down to as little as $.20/IP. The price may depend on websites you want to target and IP location.
Residential proxies are more expensive. They also have a different pricing model: instead of IPs, you’ll be paying for the traffic used. A gigabyte usually starts from $10-20, though the proxies can go for as little as $1/GB. Some providers offer unlimited traffic and charge per ports instead, but this model is less frequent.
You should note that the starting price describes entry plans. In other words, it’s actually the most you’re going to pay for proxies. As you buy more, the price of proxy servers begins dropping sharply, and it’s perfectly normal to have a 3-5 times price difference between the cheapest and most expensive plans.
Choosing a Proxy Service
When choosing proxies, we’d recommend having a solid idea what you’re going to use the proxies for. From here, you can start narrowing down the qualities of proxies that would be the most important for your tasks. Do you need a static IP or a rotating one? Is it better for you to have very fast proxies with several blocks or can you go for slower ones with fewer chances of being blocked?
If you’re still not too sure which proxies would work the best for your project, take a look at our Best Proxies list. We’ve compiled not only the best proxy providers according to types, but also according to use cases.
Or, if you’d like something easier to digest, we’ve made a short video about choosing proxies for some of the most popular use cases:
Setting Up a Proxy Server
Unlike VPNs, which have their own app and affect all your connections, you can (and sometimes have to) configure proxies with each application separately. The setup process largely depends on the software you use.
Read more: How to Set Up a Proxy Server.
Testing Proxies
When you get proxies, it’s important to test them. Most providers offer a free trial, or at least a money-back guarantee; use them. Doing so will reveal you several important things:
- If the proxy server works.
- If the IPs can access the websites you need.
- If the proxies make you anonymous.
- If they belong to the country you intended and use the right IP type.
Read more: How to Test Proxies.